Cyberwarfare continues as Russian hackers are attacking and infiltrating various government and public entities in order to aid their country’s invasion of Ukraine. After more than one month since Russia launched an attack on Ukraine, things have remained much the same.

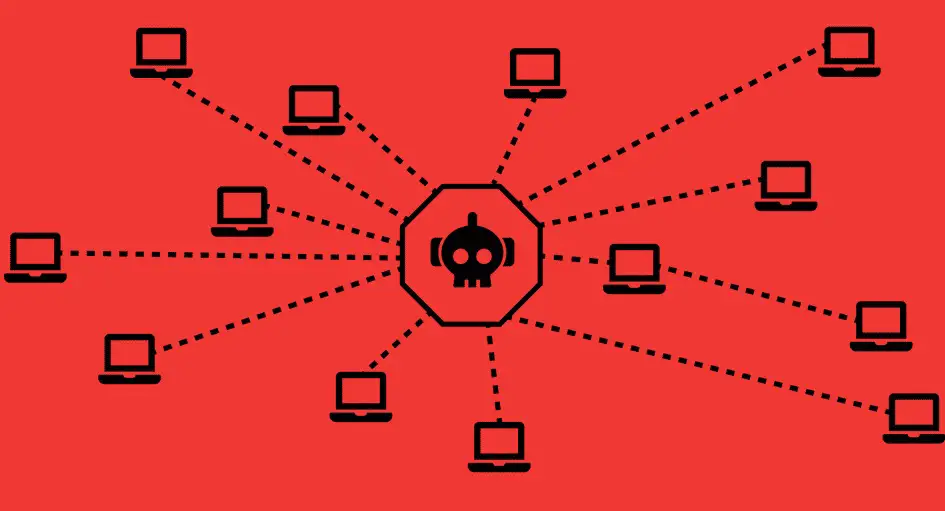
The war is taking place online as well, and the net cast by state-sponsored Russian hackers is becoming larger every day. Whether it’s attempting to break into systems to steal classified information or something worse, there are plenty of targets on the cyber front. The appearance of the Russian botnet Cyclops Blink was identified recently by cybersecurity software firm Trend Micro in a report. This is just the latest example of how such activity has become increasingly common.
What is Cyclops Blink?
According to a report by Trend Micro, a “state-sponsored botnet” known as Cyclops Blink has been operating since at least 2019 and is connected to a group dubbed Sandworm or Voodoo Bear. The group has been linked to a 2015 attack on Ukraine’s electricity infrastructure, as well as disruptions in the Republic of Georgia and at the 2018 Olympics. Firebox network security hardware appears to be the target for Voodoo Bear with Cyclops Blink, which is why Asus routers and devices from WatchGuard are being attacked. The report claims that the botnet isn’t targeting “critical organizations, or those that have an evident value in economic, political, or military espionage.”
What is the end goal for Russian hackers?
This isn’t “no harm, no foul,” though. The report claims that security experts believe Russian hackers’ main goal with Cyclops Blink is to establish a foundation for future assaults on high-value targets. Basically, Cyclops Blink was made to infect routers and use them to steal data or launch attacks against other objectives. Because they may be easier to exploit owing to less frequent updates and low-grade or no security, Asus routers with no particular military or political connection might be more readily compromised. The hacked device is used to set up remote access points for command and control servers. In the starkest terms, seemingly random seizures of devices with no apparent intelligence worth might indicate that this is the preparation for something bigger that is on its way. This creates the frightening notion of “eternal botnets,” in which machines are perpetually linked.
Asus was notified of the assaults and stated in a March 17 statement on its Product Security Advisory page that it is investigating Cyclops Blink as well as taking remediation actions. It offered a security checklist that network owners can use to increase their protection, as well as a list of all the affected devices. Cyclops Blink is so dangerous that it is advised that users who suspect infection simply replace their routers because even a factory reset won’t be enough.





